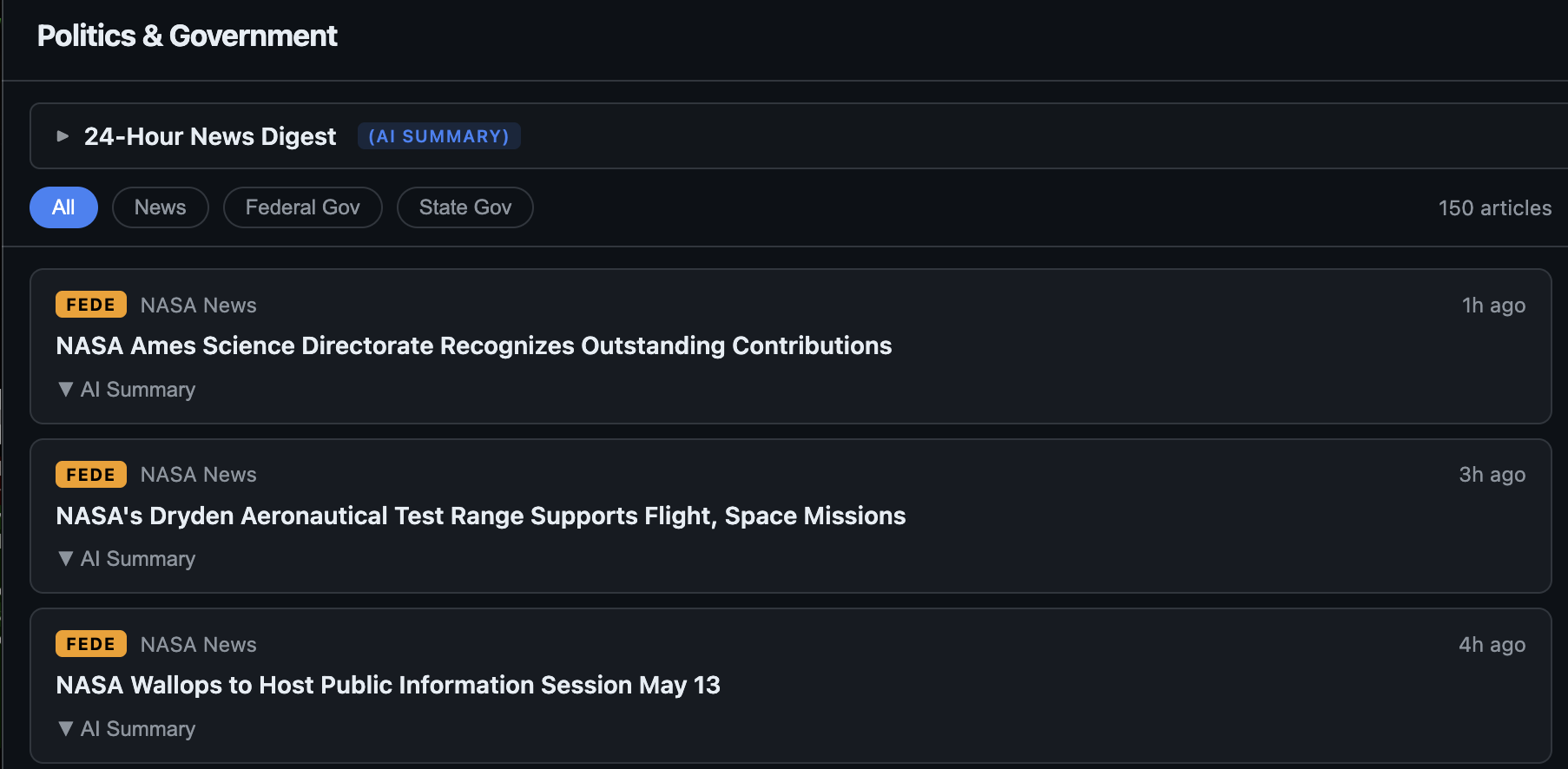
Politics Dashboard: A Self-Hosted, AI-Summarized News & X Feed Reader
Politics Dashboard: A Self-Hosted, AI-Summarized News & X Feed Reader Bottom line up front. I built and now open-sourced a self-hosted news dashboard that aggregates political news from RSS or FreshRSS, summarizes each article with a configurable LLM, generates a 24-hour thematic digest, and sits alongside live X/Twitter posts (with per-account AI summaries) via a self-hosted Nitter. Repository: github.com/RobertDWhite/politics-dashboard. License: MIT. Multi-arch images at ghcr.io/robertdwhite/politics-{api,ui}. The image I run in production is the same image GitHub Actions builds from main. ...