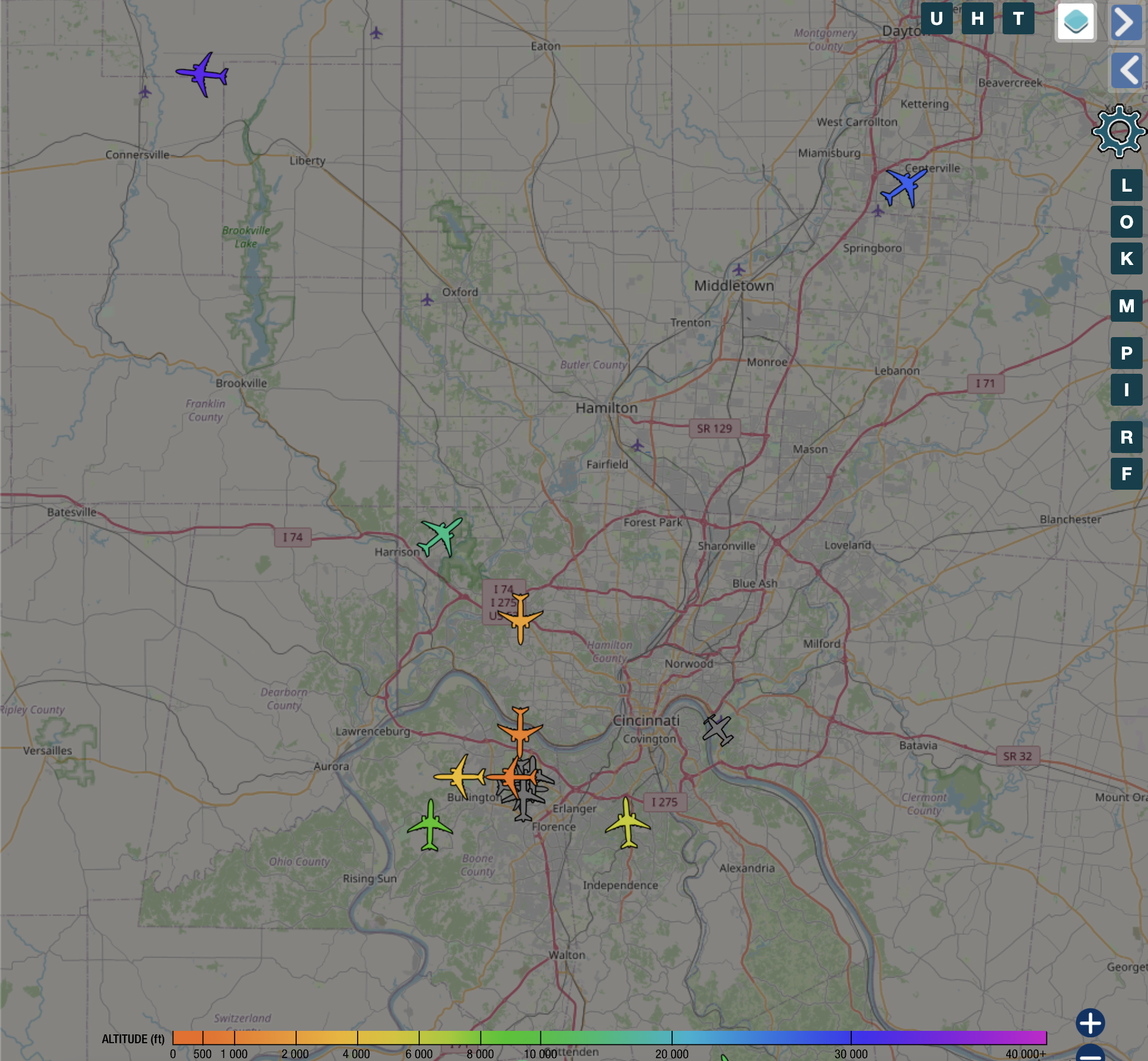
ADSB on Kubernetes
Setting Up an ADS‑B Flight Tracker with a Cheap Antenna on Kubernetes (RKE2 and ArgoCD) This is the Kubernetes version of my earlier Docker‑based ADS‑B guide. In this setup, everything is defined in YAML and deployed via ArgoCD, and changes are tracked in Git and synced automatically to the cluster. Access is handled through an NGINX Ingress with TLS from cert‑manager, which is how I publish the ADS‑B UI at adsb.w3rdw.radio. If you’re comfortable editing YAML and committing to Git, you’ll feel right at home. ...